What A Managed Security Services Provider Can Offer?
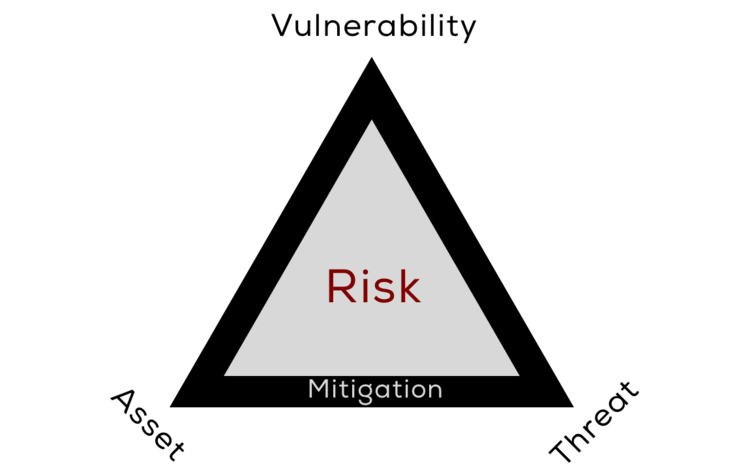
Managed security service provides analyze engineering inside your business, instead of centring very nearly singularly on dealing with your system and diverse appended gadgets.
At long last, you will likewise find that utilizing a security administration's supplier additionally helps you spare cash. System support could be time intensive and excessive. Notwithstanding, with the right supplier, you can diminish the expense here both in time and in addition in money cost. Clearly, discovering the right supplier is in your best investment. The wrong supplier may really require you cash or increment your danger level. On the other hand, with an experience, qualified organization, you will have the capacity to appreciate these key points of interest.

Managed security services, administration's supplier ought to have the capacity to guarantee that they have the most recent in engineering and that they're dependent upon pace on the latest dangers out there. At the point when evaluating such an organization, don't be reluctant to put forth extremely particular inquiries, which might be carried out without being excessively specialized. Ask them, case in point, how they might give assurance against the sorts of strike that have commanded the news of late - dispersed disavowal of administration ambushes and DNS reserve harming assaults might be great cases. They can likely clarify to you how they might go about giving your business insurance.
At last, you will likewise find that utilizing an managed security administrations supplier additionally helps you spare cash. System upkeep could be prolonged and excessive. In any case, with the right supplier, you can lessen the expense here both in time and also in money cost. Clearly, discovering the right supplier is in your best investment. The wrong supplier may really take you cash or increment your danger level. Nonetheless, with an experience, qualified organization, you will have the capacity to revel in these key favourable circumstances.
Latest Blog Post:

By Michael Samson
•
01 Nov, 2018
In an attempt to fight off the increasingly dangerous threats, cyber security firms are working nonstop to develop techniques that assist with data protection. EDR UK is one of the many techniques that is being used to block out any threats to the endpoints of system.
New Paragraph