Advantages of Outsourcing The Managed Security Services
- By Michael Samson
- •
- 17 Jul, 2018
- •

The cybercrimes are on the rise all around the world. The internet technology and networking have brought us a lot of conveniences nonetheless. But it has also been the cause of a lot of problems in shape of the cyber-crimes and threats that have been penalising business ventures all across the world.
The cybercrimes are on the rise because the negativity has increased a lot because of the internet and technology advancements over the last couple of decades. Due to this rise, different business ventures around the world have started to think seriously about the proper solution against these threats and crimes.
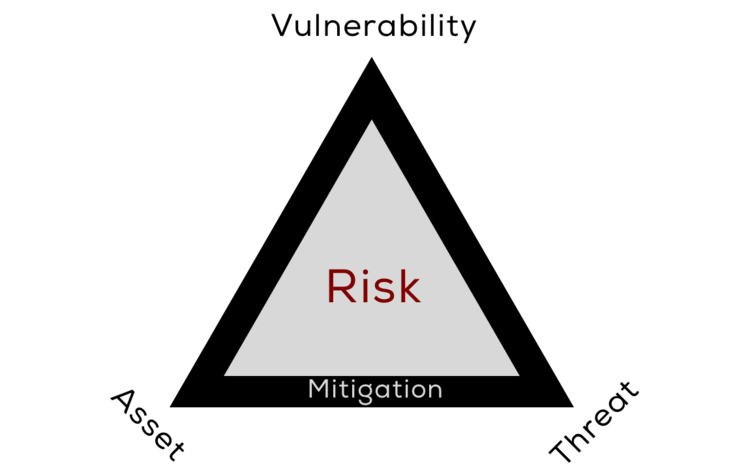
For this reason, the security threat and risk assessment process has been found quite useful in keeping these vulnerabilities away. Properly managed security services have also been helping various ventures around the world, it has some critical advantages which are as follows.
Gain Control:
By outsourcing the security services to a third party managed services provider never take away control from you. It is an entirely wrong perception because it only improves the control and helps you gain more control over your security matters.
Within your organisation, it is always challenging to take control of high-level security matters with such precision and in such an advanced way. That’s why forwarding this matter to a third party service provider can be very useful in keeping cyber-threats away to keep your business network secured.
Offensive Rather Than Defensive:
By outsourcing the security services to managed security services provider in UK can help you a great deal in remaining proactive and offensive. Your network security becomes even more hands-on rather than it is acting in a defensive mode.
Stay Updated:
That’s the only way you can stay up-to-date. At your business level, you can never remain so much updated as you could stay by outsourcing these services to MSS providers. That is the only way you stay a step beyond in the network security related matters. That’s how, the vulnerabilities, threats and cyber crimes could be effectively avoided.
Better Threat Detection and Better Actions:
The treats and vulnerabilities could be detected effectively right away. Thus, when the detection of the threats in such manner would become possible, then taking better actions against these network related threats would also be possible.