Enterprise Data Security
- By Michael Samson
- •
- 19 Dec, 2017
- •

Enterprises heavily rely on data and it is the basic element at every company’s beating heart. It is said that some of the best companies in the world would collapse in a few days due to data blackout. Being the most valuable asset of an enterprise, every possible measure is taken to keep the data safe.
Enterprises spend a lot on data security these days. Data breaches are becoming frequent and companies are not hesitant to stay ahead of the curve. Failure to observe security threat and risk assessment results in huge financial losses and a broken reputation.
Following rules are incorporated in every company’s data security policy.
Data Classification:
It is important to classify different data types and their level of sensitivity. Some of the information running through the enterprise networks is too sensitive to be leaked. Classifying the data from sensitive to normal is the first step in the process. Different data access models are also reviewed to make it more secure.
Security Policy:
Data identification and classification are just the starts. After the experts are done with the basic process, they start creating a security policy. This policy works in favor of the enterprise as data access model becomes secure and unauthorized personnel can’t even get the whiff of it. Reputable managed security services UK based companies revise security policies several times to reach the sweet spot where nothing goes unnoticed.
Experts basically determine which user, process, or application has access to the company’s sensitive data and devise methods of authentication and authorization.
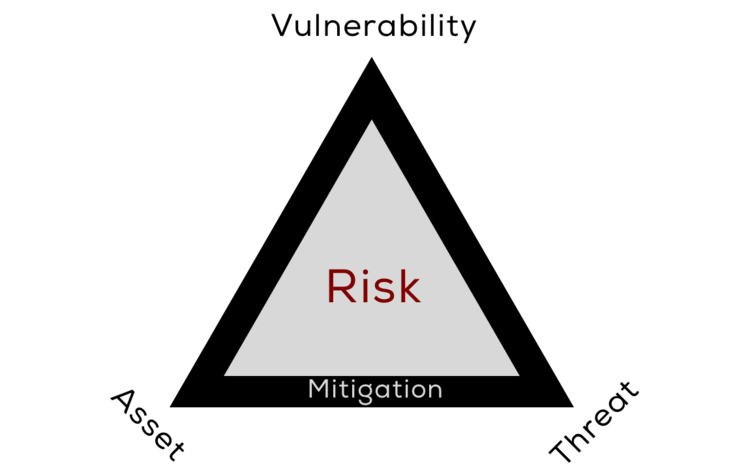
Risk Analysis:
Sometimes the level of threat is too high that immediate actions are needed. In this case, data is encrypted as soon as possible to avoid the upcoming threat and avert a bad situation. Experts have to analyze the level of threat to determine how soon they should complete their data encryption process.
Implement the Legal Measures:
Every organization has to comply with the legislative rules. This is also true in case of cyber and data security. The security experts have to work out a policy which complies with the latest rulings.
Levels of Implementation:
The new rules can be implemented at the multiple levels, but selecting the optimal level of implementation which works in favor of improving the overall security is crucial. There are four levels to implement the policies named network, database, application, and storage.
Spending Smart:
Security experts try to stay within the budget by implementing some existing technologies which support the project. It is a smart move as the implementation of the new system is expedited.