Here Is How You Select A Right Security Consulting Firm!
- By Michael Samson
- •
- 22 Sep, 2017
- •

Before finalizing and hiring the services of a consultant you must get some references from fellow companies. This will keep you safe from choosing such a consulting firm which is of no worth. That’s why, it should be a top priority for you to get references first.
Once you have some good number of references, you can then look at some collective qualities of these firms to find the best one. Because their services are what you would completely rely on for the purpose of your network security. So, it’s really vital to make sure they really worth it like the services of top-notch firm security consulting Qatar.
What network security related areas they would cover?
This should be your first and foremost important concern while you are searching for the right security consulting firm. Prepare the list of the areas where you would require their expertise. Make sure they can really help you for the security of all those required areas.
Depth of their Knowledge:
What is the depth of the knowledge of a security firm? This is another important aspect which should be considered while hiring them for your firm. Some of them have very less knowledge of the things. Whereas, some are really professional and expert. So, always make sure how deep is their knowledge in this niche?
Do they have Expertise in ELV design?
ELV design is also really important for the better functioning and continuous working of your security system which includes security cams, fire alarms and automatic fire extinguishers. With the proper ELV design all such important systems are provided with separate power sources. So in case of any mishap or emergency the most reluctant systems like these doesn’t shut down.
That’s why, it is important that your consulting firm has a firm grip over setting a proper ELV design. Otherwise, you would be required to hire the services of a separate ELV design consultant Oman Qatar, UAE or any other part of the world. Which could become an extra expense for you.
Conclusion:
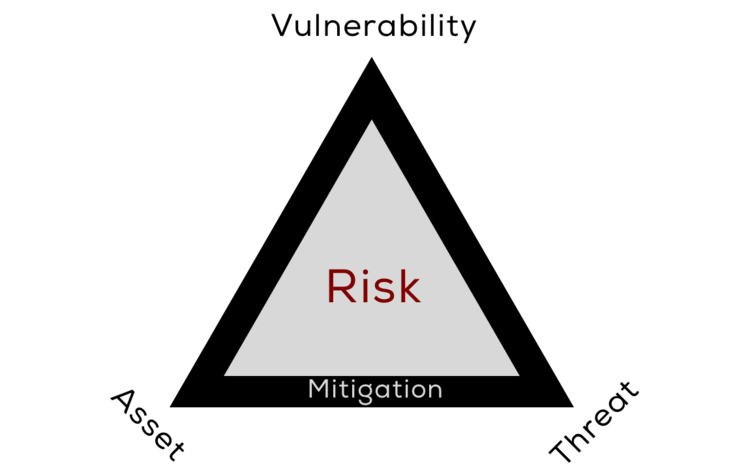
In this era, when the network vulnerabilities and threats are an extreme rise, it is really necessary for you as a firm to make proper arrangements to keep your business safe from such hazardous attacks. You can remain safe from such risks only by hiring the services of top-notch and experienced security consulting firm.