How To Manage Network Security With Specialist Consultants
- By Michael Samson
- •
- 09 Oct, 2017
- •

Introduction:
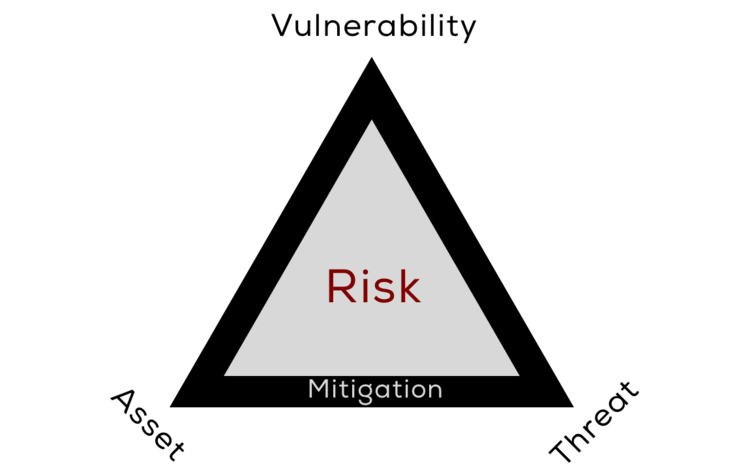
The imbalance in the security of the network can be quite detrimental. The infrastructure designed for the security is reliant on a range of different factors. How significant is your threat intelligence framework? The industry experts acknowledge the need to make radical adjustments to the security framework. In this respect the generation of intelligence from several sources can provide the difference in the outcome. The quality of the intelligence generated matters.
How to protect the network security:
Experts can categorize the significance and relational value of the information generated for security reasons. The identification of a holistic security need by UK SOC provides the structure to detect and respond to any inconsistency.
The system incorporated to address response to incidents is a dedicated endeavor. The analysis of the available data and investigation in relation to the future needs of the security must be compatible.
How the management develop the existing capability to address different security concerns is an important part of the plan. However the market is growing for the management of the security is now a key driver of developing the capabilities of dedicated security. The round the clock monitoring of the security mechanism is an expert endeavor.
In this respect the choice of security consulting KSA has the capacity to adapt to any environment to ascertain the risk supervision in different contexts.
There are quite a few regulatory requirements and experts can highlight how a comprehensive supply chain can offer better arrangement of variables to devise a mean to cover extensive security domain.
The management of different security event and their reporting procedure in a prescribed time frame is a specialist task. The different security levels designed for a range of diverse service has a major impact on the methodology of the security architecture.
Conclusion:
The access points are many on the network. The login to the system and the emergency response mechanism must be compliant with the enacted system. The communication between users across different platforms is vulnerable to breach. There are different indicators that ascertain the value of relationship across various communication platform.
The recognition of the usual patterns of security is important in delineating how the system operate as a unit. You need to envision how carefully each access point is monitored. The managed monitoring service can provide the balance to ensure any susceptibility is immediately identified and responded with diligence.