How To Penetrate Security Features With Managed Diligence
- By Michael Samson
- •
- 05 Sep, 2017
- •

The recognition of the potential defective sources is important:
The security leverage is only realizable when due diligence is practiced. For that you will have to adhere to best practices. Sometimes the organization does not have the resources to fulfill the notion of due diligence. The orientation of technological tool and the direction it provides to the outcome of the security is an undeniable necessity. Different tests carried out to monitor the existing potency of the security along with any potential loophole must be identified.
Experts can resolve the matter:
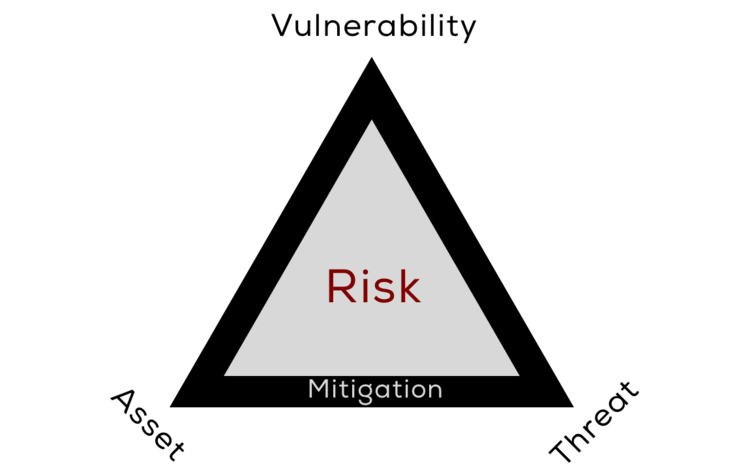
The interdependency of the variables makes it imminent to identify how different aspects of security can be launched in its entirety. Understanding the emerging trends is important but it is not enough. You can’t realize the objective without contextual planning. Each security program is derived from a specific reason by penetration testing Dubai. The grounds to develop the basis for a security program must be valued at different intervals. The security outcome will be pointless and the resources will be wasted. The accurate positioning of the resources is achievable when a reachable roadmap is constructed. What activate a specific security threshold must be addressed in diverse perspectives. The foundation of security challenges must validate the initiation of the protection plan.
The general feeling is that all is good since a tool has been incorporated. This is simply over the board thinking especially when the business success is at stake. How you anticipated a fabricated potential lie? The cost of business loss is far elevated in comparison to the monetary resource spent on buying the security tool. Whatever security sensitivity may emerge in future can be addressed by managed security services Qatar.
Right now, you cannot derive security relief:
It is understandable. The gravity of insecurity is overbearing. It is so much more that the business can bear. But yes you did made the choice. You are the centre of attraction for the stakeholders. The customers pin their hopes on you. It is an obligation to ensure customer information is secure. Prioritize how an efficient response mechanism can be designed to address the varying nature of security. The targeted breaches are on the rise. Experts believe that 2018 will witness the rise of highly sensitive security tools that disallow any type of penetration. The rising trend of mobile usage is a prime instance of how security aspects will go beyond imagination.