How Important Is The Penetration Testing?
- By Michael Samson
- •
- 26 May, 2017
- •
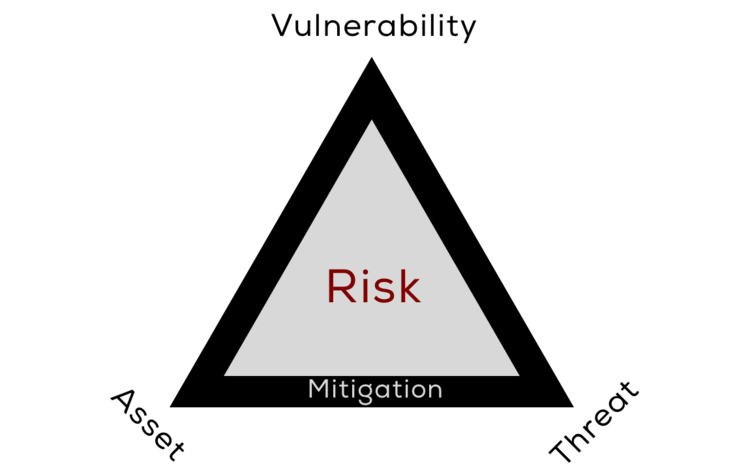
Penetration testing is done to test your network for any possible threats and vulnerabilities. We know that, the networks these days are surrounded by different threats. So the businesses and other firms need to keep themselves safe from these threats and risks to ensure that they are in a safe zone.
During the penetration testing, a network is being tested by a team of professional testers. That includes hackers, networking experts, and other IT specialists. No secret information is being exposed to them to ensure that they can hack the network and find its flaws on their own.
They
put up their efforts to somehow make it possible to attack and hack the network
they are working on. That attack and hacking help them know the weak points.
That’s how the testing of a network is done. The penetration testing Dubai
are well-known for their expert services
in this niche.
How Penetration Testing could be done?
It can be done in following ways.
Company Address:
Web Application:
Why is this test important?
It is really important for an organization to put their application or network in front of a professional team which can try to find out what weak points does it have? They put their efforts to try to hack and compromise the security somehow.
Whenever a network or a security application is built, it possibly can have some weak points. It is important for the company to know them. But they can never test and know the flaws well on their own. That’s why, a professional testing team is hired as they are experienced hackers, so they somehow find all the possible weak points.
Conclusion:
The penetration testing is common these days all around the world. Companies do prefer it a great deal now, to remain safe from the threats and hackers. Thus, with the standard ISO 270001 Oman has a lot of information security providing and testing firms. They help the organizations to remain safe from different threats and vulnerabilities.