VAPT Testing, For Improved Awareness And Timely Response!
- By Michael Samson
- •
- 03 Aug, 2017
- •

Introduction:
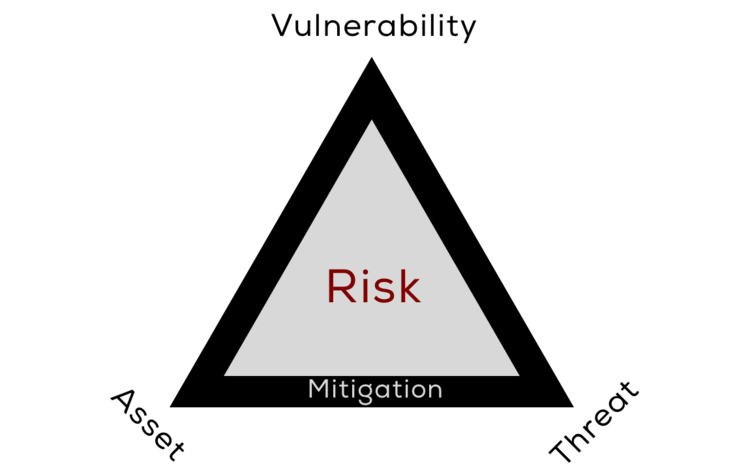
Business world online has been always vulnerable to cyber attacks. Despite the fact that technological trends are advancing with consistency, it seems that the attackers are also no ready to give up on improving their skills. Moving on and running a business online in such situations can be at times a very tricky choice.
A secured approach:
Rather than rely on free anti-viruses and firewall that may often not work, one simply should consult with expert security solution providers. The problem with free security softwares is that they are very low on protection and may easily be compromised. They are limited in nature and even if they are up to date, they may not help in comprehensive protection.
Entrepreneurs who run companies that rely on interconnected systems and networks are aware that they cannot afford to move on with weaker security measure. Such approaches may dent their business’s sensitive data and they may even find it hard to secure the sensitive information associated with their clients.
Expert security solution providers therefore highly recommend vulnerability and penetration VAPT testing. These tests enable one to figure out the gaps that may be present and may provide opportunities to hackers to break into the system.
Dealing with such advanced technologies with an in-house approach may not be feasible in many ways. To start with, in-house personnel may not be available 24/7. They in addition may not be very well versed when it comes to deal with such critical situations. Their limited knowledge may brighten the chances for hackers and attackers to break in.
It is therefore highly recommended that one should consider the idea of outsourcing these highly critical tasks to those that are professionals. Managed SIEM solutions are normally the right way to go about things in this domain. With the influx of latest technologies like artificial intelligence and virtual reality, business owners can get hands on solutions in real time.
Conclusion:
To achieve great results when it comes to ROIs, one would need to focus on business and to do so, it would be great if one can outsource all the time consuming and sensitive tasks like managing information security and event management tasks to third parties that are renowned for delivering such services in a professional and affordable passion.
Failing on this approach would mean getting stuck on a point that is deviating one from goals like ensuring better conversions and amplification of business growth.