Load Of Designing Security Mechanism Is Heavy, Let Specialists Do It
- By Michael Samson
- •
- 18 Aug, 2017
- •

Introduction:
The interface designed to manage load is an important part of engineering solutions for buildings. The infrastructure must address the cabling needs. The level of susceptibility is high. Efficient cabling solutions address how to design the most optimum methodology.
Clear out any possible mess:
Load distribution should correspond with spatial distribution. The distribution of the load and the modular design must also undertake the probability of failure. In any case the extended methodology must ascertain how sustainable power supply can be incorporated in the infrastructure. What you can’t do is taking unnecessary risks for the sake of saving cost.
The extension of different possibilities can be augmented by ELV design consultant Oman.
It would be beneficial to manage the security issues in an all-encompassing manner. How much time and effort is dedicated to security issues will eventually payback. Isn’t it interesting that the return on investment for security features are accrued after lengthy time period. The discussion related to the surroundings of security must entail how feasible outcomes can be achieved that address the realities based on a dedicated methodology.
And so we have to say that no chances can be taken where security is under consideration. Before we deploy the security parameters advice can be of assistance; security consulting qatar can provide the roadmap of security.
How to plan and why?
The planning related to the requirements of infrastructure and deployment of the right set of resources is reliant on conditional planning. You get the best outcome only when its fits with your needs.
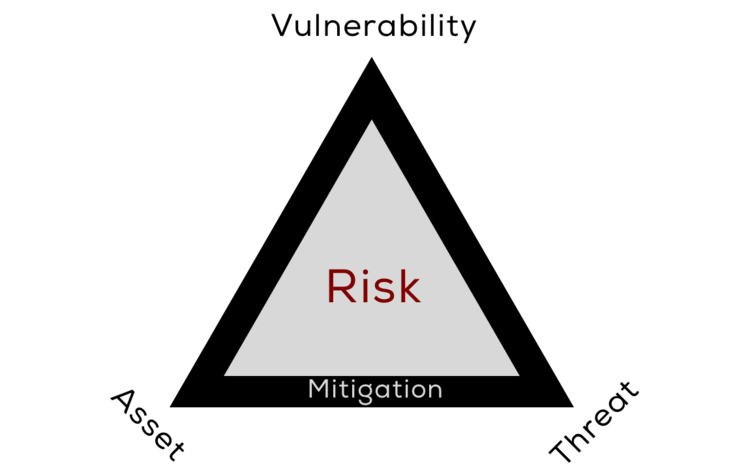
Experts can improve the probability of effectively realizing efficient outcomes that augment the productivity. The different point of contact can push the security parameters out of bound. Many plan fail to address ‘why’ a specific methodology is being enforced. This can leave gaping holes and the cracks may surface up in future.
Conclusion:
The questions relating to security issues are unlimited. What type of features should be incorporated by you? What is the biggest strength of the security mechanism? How do you identify the greatest weakness of the security framework? All the above mentioned questions requisite all-encompassing justification of the choice of the service that is being incorporated. That is what viable businesses do. They go for precision to avoid contamination of outcomes. Experts can dig out the best security solution for different types of requirements.