Manage Security Of Data With Cloud Services
- By Michael Samson
- •
- 11 Aug, 2017
- •

Introduction:
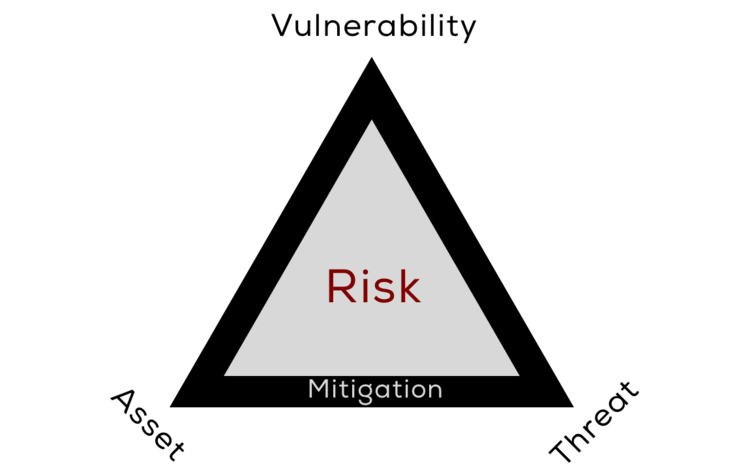
Enterprise solution to safeguard the security of the network is a mainstream issue for any company in whatever industry. The solution must be al-embracing. It should incorporate different software as well as hardware appliances to create a genuine security structure that features detailed protection mechanism for diversified type of threats.
The multiple threat analysis:
In the presence of multiple threats a detailed analysis must be carried out to outline how each element can contribute towards network security. The focus of managed security services Dubai is to leverage the security needs of the system with user compatibility.
Why distribute resources judiciously:
Allocating the resources on data protection is also important to consistently monitor its movement across the network. The capability to build capacity in securing data is reliant on the developed infrastructure. Many small and medium sized firms are unable to build the desired infrastructure.
Third party intervention in securing data can offer better control of the security. This is important in avoiding legal proceedings. Additionally any leakage of sensitive information is a big loss to the reputation of the company.
The focused approach in securing data can be provisioned by cloud security services.
Data sharing security parameters also requisite addressing the issue in its entirety. The banking, insurance as well as the retail sector are the favorite destinations of hackers. The protection of data through third party is a growing trend.
Comply fully with the trends:
The compliance procedures warrant an effortless and risk free monitoring of the data. As cyber-attacks have multiplied in numbers it would be logical to disrupt any advance of the hackers in whatever capacity. Have you thought about it? Try to evade any legal proceedings. Invest in a sensible security mechanism that offer the value for money. Prepare for any extreme potential threat to the network.
Design sustainable security parameters:
The evaluation entailing the security framework should engage different possibilities that leads to data infiltration. The crux of a comprehensive security framework is its ability to design flexibility to update any potential future need. This is a cost sensitive area and can help in saving plenty of monetary resources.
Conclusion:
The investigation into data security reveals that the breakdown of the existing and the strategic needs must be incorporated in the framework. Engage the expert after serious contemplation and the risk involved in case of breach.
Somebody has to be held accountable in case of breach. This cannot go on like this, forever.